UDP
|
Topics: |
The User Datagram Protocol (UDP) is a transport layer protocol defined for use with the Internet Protocol (IP) network layer protocol. UDP is one of the core members of the IP suite. UDP uses a simple connectionless transmission model with a minimum of protocol mechanism. Unlike TCP/IP, UDP/IP provides very few error recovery services, offering instead a direct way to send and receive messages over an IP network. It is used primarily for broadcasting messages over a network.
UDP performs no handshaking between the sending and receiving parties and is therefore said to be connectionless. This protocol does not maintain state. As a result, it is fast and light-weight in terms of system resource usage. Lack of error handling and packet organization (packets can arrive in any order) make UDP useful for implementing very fast, lightweight services, such as lookups. In fact, the DNS service of the Internet is implemented using UDP.
You can listen for incoming UDP message packets by using the UDP listener, and can emit UDP message packets through the UDP Emitter or the UDP Emit service (com.ibi.agents.XDUDPEmitAgent).
Configuring the UDP Listener
You can listen for inbound UDP requests by configuring the UDP listener.
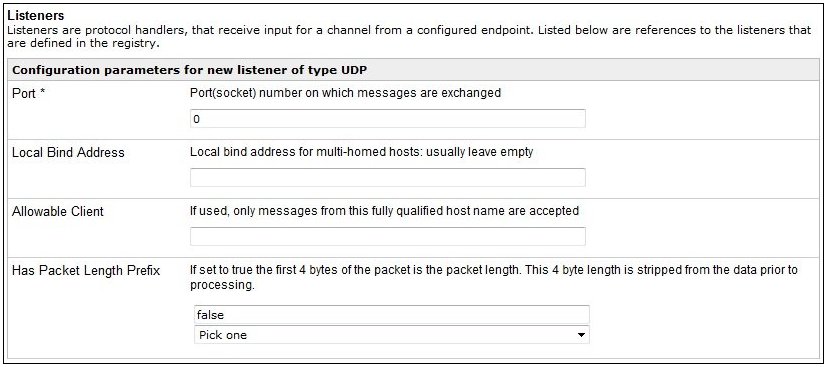
The following table lists and describes the configuration parameters for the UDP listener.
|
Parameter |
Description |
|---|---|
|
Port * |
The active port on which the UDP message packet will be received. |
|
Local Bind Address |
This parameter reserved for instances of iSM that are installed on machines where multiple network adapters are installed. This parameter allows you to configure the UDP listener to use a different IP address than the default address of the system. |
|
Allowable Client |
This parameter allows you to restrict the source of the UDP message to a specific host address. This field is a comma-separated listing of host names and IP address filters that will be applied to the source address of the UDP packet. If the packet source does not match one of the filters, then the packet is rejected. The filters support wild card characters, for example, an asterisk (‘*’), any grouping of one or more characters, and any single character (‘?’). Sample Filters:
Note: Using a host name string pattern will force a DNS lookup on the sender name of the UDP message packet. This may be time consuming if your DNS cache is not up to date. However, using an IP Address string pattern does not require a DNS lookup and should be faster. |
|
Has Packet Length Prefix |
Determines whether to prepend the data packet length. Select one of the following values from the drop-down list.
By default, false is selected. |
|
Tuning |
|
|
Multithreading |
Indicates the number of worker threads (documents or requests) that iWay Service Manager can handle in parallel. Setting this to a value of greater than 1 enables the listener to handle a second request while an earlier request is still being processed. The total throughput of a system can be affected by the number of threads operating. Increasing the number of parallel operations may not necessarily improve throughput. The default is 1. The max value is 99. |
|
Optimize Favoring |
Use this option to customize how the listener performs. For smaller transactions, select performance. For large input documents that could monopolize the amount of memory used by iWay Service Manager, select memory. |
|
Polling Interval |
The maximum wait interval (in seconds) between checks for new requests or commands. The higher this value, the longer the interval, and the fewer system resources that are used. The side effect of a high value is that the worker thread will not be able to respond to a stop command. The default is 2.0 seconds. |
|
Events |
|
|
Expired Retry Flow |
Name of a published process flow to run if a message on the retry queue has expired. |
|
Failed ReplyTo Flow |
Name of a published process flow to run if a message cannot be emitted on an address in its reply address list. |
|
Dead Letter Flow |
Name of a published process flow to run if an error cannot be emitted on an address in its error address list. |
|
Channel Failure Flow |
Name of a published process flow to run if this channel cannot start or fails during message handling. iWay Service Manager will attempt to call this process flow during channel shut down due to the error. |
|
Parse Failure Flow |
Name of published process flow to run if XML parsing fails for incoming message. |
|
Channel Startup Flow |
Name of published process flow to run prior to starting the channel. |
|
Channel Shutdown Flow |
Name of published process flow to run when the channel is shut down. |
|
Other |
|
|
Whitespace Normalization |
Specifies how the parser treats whitespace in Element content. Choose preserve to turn off all normalization as prescribed by the XML Specification. Choose condense to remove extra whitespace in pretty printed documents and for compatibility with earlier versions. |
|
Accepts non-XML (flat) only |
If set to true, the input data is sent directly to the business logic step. The data is not preparsed, parsed, or validated. This flag is used primarily to send non-XML to the business logic or replyTo without processing it. |
|
Execution Time Limit |
The maximum time that a request may take to complete. Used to prevent runaway requests. Any request that takes longer to complete than this value will be attempted to be terminated. |
|
Default Java File Encoding |
The default encoding if incoming message is not self-declaring (that is, XML). |
|
Agent Precedence |
Sets the order by which iWay Service Manager selects agents. iWay Service Manager selects the agent or agents to process the document by searching through the configuration dictionary. Usually, it looks for a document entry in the configuration and when a match is found, the agent specified in that document entry is selected. If a matching document entry is not found, or no agent is specified, the engine looks in the input protocol configuration (listener). To have the processing agent taken directly from the listener (thus ignoring the document entry), use <listener> overrides <document>. Possible values are <document> overrides <listener> and <listener> overrides <document>. The default value is <document> overrides <listener>. |
|
Always reply to listener default |
If set to true, the default reply definition is used in addition to defined reply-to and error-to destinations. |
|
Error Documents treated normally |
If set to true, error documents are processed by any configured preemitters. |
|
Listener is Transaction Manager |
If set to true, agents run within a local transaction. |
|
Record in Activity Log(s) |
If set to true, activity on this channel will be recorded in the activity logs, otherwise the activity will not be recorded. |
|
AES Key |
If the channel will receive encrypted AFTI messages, set the AES key (maximum 16 characters) to be used for decrypting. |
|
Startup Dependencies |
A comma-separated list of channel names that must be started before this one is called. |
Configuring the UDP Emitter
You can emit UDP replies or requests by configuring the UDP emitter.
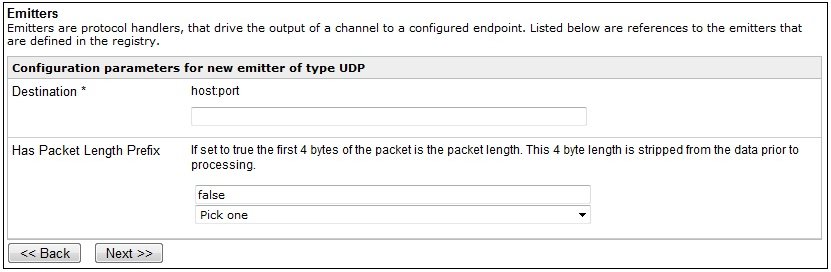
The following table lists and describes the configuration parameters for the UDP emitter.
|
Parameter |
Description |
|---|---|
|
Destination * |
The host and port destination where the UDP message packet will be transmitted. The entry is in the form of host:port. For example, reporter:1234 to route messages to the reporter machine on port 1234. |
|
Has Packet Length Prefix |
Determines whether to prepend the data packet length. Select one of the following values from the drop-down list.
By default, false is selected. |
Configuring the UDP Emit Service
The UDP Emit service allows you to configure a service to transmit a User Datagram Protocol (UDP) message packet to a specified host.
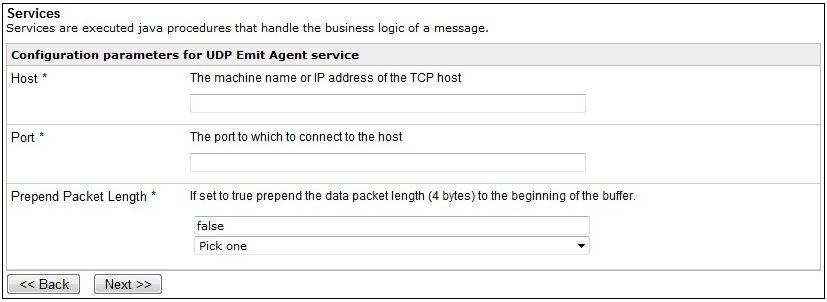
Syntax:
com.ibi.agents.XDUDPEmitAgent
Parameters:
|
Parameter |
Description |
|---|---|
|
Host |
The host name or IP address of the machine to which the UDP message packet will be sent. |
|
Port |
The port number of the host to which the UDP message packet will be sent. |
|
Prepend Packet Length |
Determines whether to prepend the data packet length. Select one of the following values from the drop-down list.
By default, false is selected. |
Note: Due to the nature of UDP, the only error checking that is performed is whether the host machine can be reached. Message packets are sent to the host with no guarantee that the packet was received or was processed by the specified host system.